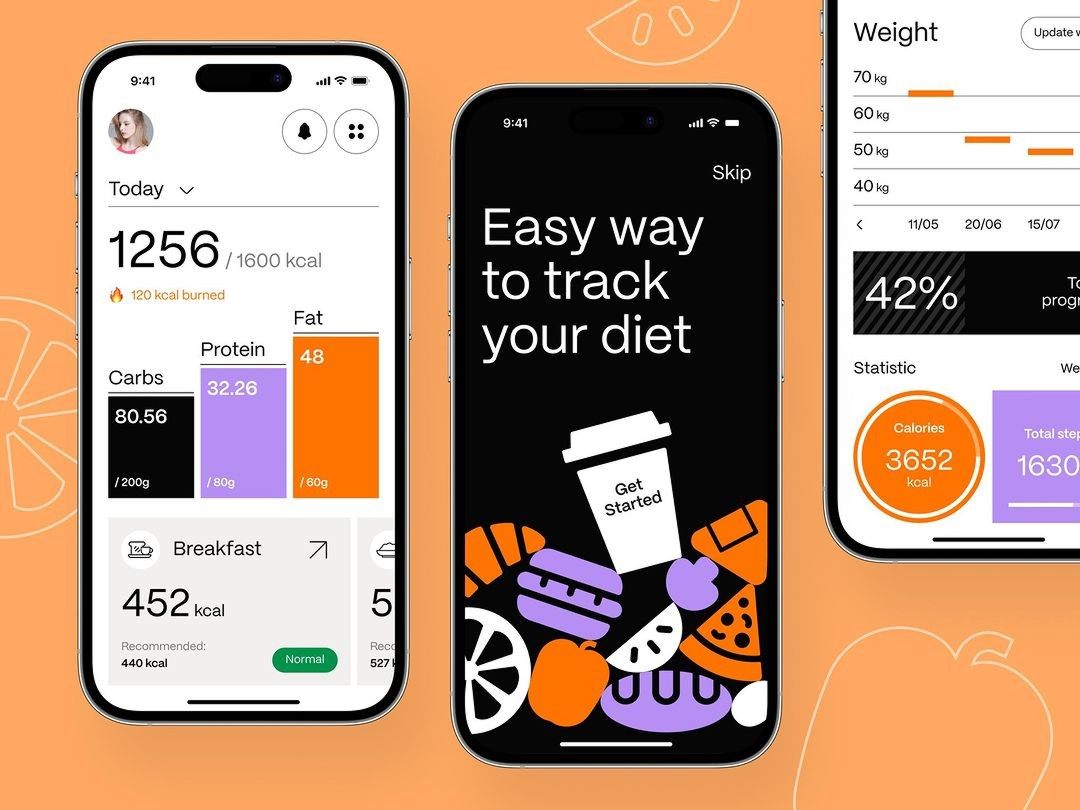
The Ultimate Guide to Byjus Clone App: Key Benefits & Features
Byjus Clone App: Key Features, Benefits, and Cost Breakdown for Your Business Launch your own Byjus clone app with interactive learning features, customizable options, and scalable architecture for modern edtech platforms. Talk To Our Experts Professional Byjus clone app development is revolutionizing the global education sector by offering scalable digital learning environments for millions of […]
Coinbase Clone App: Unlocking Key Features and Business Benefits

Coinbase Clone App: Key Features, Benefits, and Cost Breakdown for Your Business Launch your own Coinbase clone app with secure crypto trading features, customizable options, and scalable architecture for modern exchange platforms. Talk To Our Experts In the rapidly evolving digital economy, establishing a reliable cryptocurrency exchange is a strategic move for entrepreneurs looking to […]
Mobile App Development Benefits in Santa Clara

Key Benefits of Mobile App Development in Santa Clara Mobile app development in Santa Clara businesses improve customer engagement, streamline operations, and deliver seamless digital experiences across iOS and Android platforms. Talk To Our Experts Securing high-quality mobile app development benefits Santa Clara companies by bridging the gap between complex backend systems and the palm of […]
Key Benefits Web Development Services in Solvang

Benefits and Features of Web Development Services in Solvang Web development services in Solvang offer a multitude of benefits that can significantly enhance the online presence and functionality of your business. Talk To Our Experts Securing top-tier web development services in Solvang is the most effective way for local businesses to establish a high-authority digital presence […]
Anthropic Introduces Mythos AI Model in New Cybersecurity Initiative

Summary Anthropic launches the Mythos model to redefine proactive network defense strategies. Leading providers like Amazon and Microsoft supply the infrastructure for this AI rollout. New Security protocols focus on neutralizing complex threats within the global Enterprise landscape. Specialized training allows the system to identify malicious code patterns before exploitation occurs. Ethical guardrails ensure these […]